Imagine it’s 2 AM. Your healthtech application, which monitors real-time patient vitals across fifty hospitals, suddenly experiences a 400% spike in traffic due to a seasonal flu outbreak. Your on-premise servers are sweating, spinning at maximum capacity, and on the brink of crashing. If they go down, doctors lose data. But if you blindly migrate everything to a public cloud to handle the load, you risk violating strict healthcare data privacy laws, potentially facing millions of dollars in compliance fines.
This isn’t a hypothetical nightmare; it’s a situation I walked into during my fourth year as a infrastructure architect. We were trapped between the rigid walls of data security and the unpredictable demands of scalability.
That was the night I stopped looking at IT infrastructure as an “either/or” choice. In my ten years of navigating the shifts in tech, nothing has revolutionized the digital landscape quite like hybrid cloud computing. It is the ultimate bridge for companies that need the freedom to scale without losing their grip on governance.
Let’s take a deep dive into how a hybrid cloud works, why it is the sweet spot for modern businesses, and how you can strike that perfect balance between flexibility and control.
What is Hybrid Cloud Computing Anyway?
To understand hybrid cloud computing, let’s step away from the server room and walk into a kitchen.
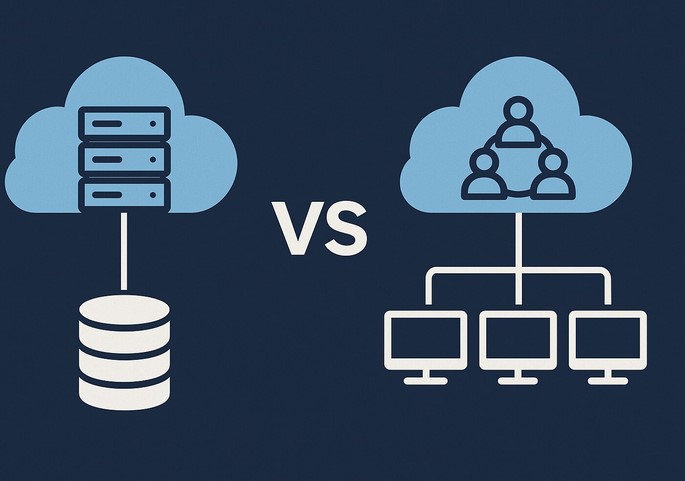
Think of a private cloud (or your local on-premise data center) like your home kitchen. You own the appliances, you control who cooks, and you know exactly how clean the counters are. It’s highly secure and customized, but if you suddenly need to host a banquet for 500 people, your small kitchen will fail miserably.
On the flip side, a public cloud (like AWS, Google Cloud, or Microsoft Azure) is like a massive commercial catering service. You don’t own the kitchen, but you can order as much food as you want, instantly, to feed thousands. It’s incredibly flexible, but you don’t have total control over how the ingredients are handled.
A hybrid cloud computing environment is having both. You cook your secret, signature family recipes in your private kitchen (your sensitive data), but you use the catering service to handle the side dishes and extra guests when things get busy (cloud bursting).
Technically speaking, it is an IT architecture that orchestrates a mix of on-premises infrastructure, private cloud services, and public cloud platforms, bound together by standardized technology that allows data and applications to move seamlessly between them.
The Tug-of-War: Flexibility vs. Control
In my experience, tech deployments usually suffer from a cultural tug-of-war. Developers crave flexibility; they want to build, test, and scale applications using cutting-edge public cloud services without waiting for hardware procurement. On the other hand, the Compliance and Security teams demand control; they want to know exactly which physical hard drive holds their users’ sensitive information.
If you lean too far toward the public cloud, you risk vendor lock-in, unpredictable data egress fees, and potential compliance headaches with frameworks like HIPAA or GDPR. If you lock yourself in a private data center, you miss out on rapid deployment, advanced AI analytics tools, and global reach.
Hybrid cloud computing resolves this tension. It acknowledges that not all workloads are created equal:
-
For the Core Assets: Your core databases, legacy systems, and highly regulated data stay inside your private environment under your direct supervision.
-
For the Innovation Engine: Your customer-facing apps, testing environments, and heavy analytical processing leverage the raw power and elastic nature of the public cloud.
Behind the Scenes: The Technical Glue
How do these two vastly different worlds actually talk to each other without creating a chaotic mess? It comes down to a few critical LSI technologies that we use to keep things synchronized:
1. Containerization and Kubernetes
In the early days, moving an application from an on-premise server to the cloud required massive code rewrites. Today, we use containers (like Docker) to package applications with everything they need to run. Kubernetes then acts as the conductor, orchestrating these containers seamlessly across both private and public environments. If it runs on your local machine, it will run on AWS exactly the same way.
2. Robust API Integration
Application Programming Interfaces (APIs) are the digital highways connecting your environments. They allow software components in the public cloud to securely query data residing in your private database without requiring the entire dataset to move.
3. Unified Management Platforms
You cannot manage a hybrid environment using five different dashboards. Modern infrastructure relies on unified management planes (like Azure Arc, Google Anthos, or AWS Outposts) to provide a single pane of glass view, allowing your DevOps teams to monitor performance, security, and costs everywhere at once.
The Hidden Caveats: What They Don’t Tell You in the Brochure
While the benefits are massive, setting up a hybrid cloud computing architecture isn’t a walk in the park. Over the past decade, I’ve seen many brilliant teams stumble over the same hidden hurdles.
Pro Tip: Watch the Network Latency
Just because your public cloud and private cloud can talk to each other doesn’t mean they do it instantly. If your application logic lives in the public cloud but needs to make a thousand database calls per second to a private server on the other side of the country, latency will kill your user experience. Always place your interconnected workloads as geographically close as possible, and invest in dedicated, high-speed connections like AWS Direct Connect or Azure ExpressRoute.
Another major challenge is Cloud Data Fragmentation. When data lives in multiple places, maintaining a “single source of truth” becomes incredibly difficult. Without strict data governance policies, you run the risk of running analytics on outdated or duplicated information.
Is a Hybrid Strategy Right for You?
If you are a startup launching a simple, non-regulated mobile game, a 100% public cloud route is likely your best, cheapest bet.
However, you should seriously consider a hybrid model if you meet any of the following criteria:
-
Strict Regulatory Compliance: You handle healthcare, financial, or legal records that require local residency or specialized physical security.
-
Legacy Modernization: You have massive, older ERP systems that are too expensive or risky to migrate entirely to the cloud, but you still want to build modern web front-ends for them.
-
Dynamic Workloads: Your business experiences massive, predictable or unpredictable swings in traffic (e.g., e-commerce sites during Black Friday, or telehealth apps during a health crisis).
Conclusion: Crafting Your Balanced Future
Achieving the perfect balance between flexibility and control is not a one-time setup; it is an ongoing journey. Hybrid cloud computing gives you the unique architectural sovereignty to write your own rules, scale on demand, and sleep peacefully at night knowing your most valuable digital assets are safely locked in your vault.
Don’t let the complexity intimidate you. Start small—perhaps by moving your disaster recovery or application testing environments to the public cloud while keeping your production core at home—and scale your hybrid footprint as your team’s confidence grows.
What about your organization? Are you currently leaning more toward total cloud freedom, or are you keeping things close to home? What is the biggest roadblock you’ve faced while trying to bridge the gap? Drop your thoughts, experiences, or questions in the comments below—let’s start a conversation!